About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 913 results for "Gert Jan Kramer" clear search
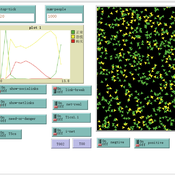
Peer reviewed Agent-based model to simulate equilibria and regime shifts emerged in lake ecosystems
no contributors listed | Published Tuesday, January 25, 2022(An empty output folder named “NETLOGOexperiment” in the same location with the LAKEOBS_MIX.nlogo file is required before the model can be run properly)
The model is motivated by regime shifts (i.e. abrupt and persistent transition) revealed in the previous paleoecological study of Taibai Lake. The aim of this model is to improve a general understanding of the mechanism of emergent nonlinear shifts in complex systems. Prelimnary calibration and validation is done against survey data in MLYB lakes. Dynamic population changes of function groups can be simulated and observed on the Netlogo interface.
Main functional groups in lake ecosystems were modelled as super-individuals in a space where they interact with each other. They are phytoplankton, zooplankton, submerged macrophyte, planktivorous fish, herbivorous fish and piscivorous fish. The relationships between these functional groups include predation (e.g. zooplankton-phytoplankton), competition (phytoplankton-macrophyte) and protection (macrophyte-zooplankton). Each individual has properties in size, mass, energy, and age as physiological variables and reproduce or die according to predefined criteria. A system dynamic model was integrated to simulate external drivers.
Set biological and environmental parameters using the green sliders first. If the data of simulation are to be logged, set “Logdata” as true and input the name of the file you want the spreadsheet(.csv) to be called. You will need create an empty folder called “NETLOGOexperiment” in the same level and location with the LAKEOBS_MIX.nlogo file. Press “setup” to initialise the system and “go” to start life cycles.
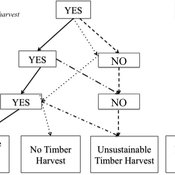
Private forest owner management behavior using social interactions, information flow, and peer-to-peer n
Jessica Leahy Emily Silver Huff Aaron R Weiskittel Caroline L Noblet David Hiebeler | Published Tuesday, October 13, 2015This theoretical model includes forested polygons and three types of agents: forest landowners, foresters, and peer leaders. Agent rules and characteristics were parameterized from existing literature and an empirical survey of forest landowners.
Peer reviewed Coupled demographic dynamics of herd and household in pastoral systems
Mark Moritz Ian M Hamilton Andrew Yoak Abigail Buffington Chelsea E Hunter Daniel C Peart | Published Saturday, April 08, 2023This purpose of this model is to understand how the coupled demographic dynamics of herds and households constrain the growth of livestock populations in pastoral systems.
Peer reviewed Co-adoption of low-carbon household energy technologies
Mart van der Kam Maria Lagomarsino Elie Azar Ulf Hahnel David Parra | Published Tuesday, August 29, 2023 | Last modified Friday, February 23, 2024The model simulates the diffusion of four low-carbon energy technologies among households: photovoltaic (PV) solar panels, electric vehicles (EVs), heat pumps, and home batteries. We model household decision making as the decision marking of one person, the agent. The agent decides whether to adopt these technologies. Hereby, the model can be used to study co-adoption behaviour, thereby going beyond traditional diffusion models that focus on the adop-tion of single technologies. The combination of these technologies is of particular interest be-cause (1) using the energy generated by PV solar panels for EVs and heat pumps can reduce emissions associated with transport and heating, respectively, and (2) EVs, heat pumps, and home batteries can help to integrate PV solar panels in local electricity grids by offering flexible demand (EVs and heat pumps) and energy storage (home batteries and EVs), thereby reducing grid impacts and associated upgrading costs.
The purpose of the model is to represent realistic adoption and co-adoption behaviour. This is achieved by grounding the decision model on the risks-as-feelings model (Loewenstein et al., 2001), theory from environmental and social psychology, and empirically informing agent be-haviour by survey-data among 1469 people in the Swiss region Romandie.
The model can be used to construct scenarios for the diffusion of the four low-carbon energy technologies depending on different contexts, and as a virtual experimentation environment for ex ante evaluation of policy interventions to stimulate adoption and co-adoption.
Do microfinance institutes help slum-dwellers in coping with frequent disasters? An Agent-Based Modelling study
Mitali Yeshwant Yeshwant Joshi | Published Friday, March 13, 2020The model aims to investigate the role of Microfinance Institutes (MFIs) in strengthening the coping capacity of slum-dwellers (residents) in case of frequent disasters. The main purpose of the model is system understanding. It aids in understanding the following research question: Are the microcredits provided by MFI to start a small business helpful in increasing coping capacity of a slum dweller for recovering from frequent and intense disasters?
DARTS: an agent-based model of the global food system for studying its resilience to shocks
Hubert Fonteijn | Published Wednesday, November 22, 2023DARTS simulates food systems in which agents produce, consume and trade food. Here, food is a summary item that roughly corresponds to commodity food types (e.g. rice). No other food types are taken into account. Each food system (World) consists of its own distribution of agents, regions and connections between agents. Agents differ in their ability to produce food, earn off-farm income and trade food. The agents aim to satisfy their food requirements (which are fixed and equal across agents) by either their own food production or by food purchases. Each simulation step represents one month, in which agents can produce (if they have productive capacity and it is a harvest month for their region), earn off-farm income, trade food (both buy and sell) and consume food. We evaluate the performance of the food system by averaging the agents’ food satisfaction, which is defined as the ratio of the food consumed by each agent at the end of each month divided by her food requirement. At each step, any of the abovementioned attributes related to the agents’ ability to satisfy their food requirement can (temporarily) be shocked. These shocks include reducing the amount of food they produce, removing their ability to trade locally or internationally and reducing their cash savings. Food satisfaction is quantified (both immediately after the shock and in the year following the shock) to evaluate food security of a particular food system, both at the level of agent types (e.g. the urban poor and the rural poor) and at the systems level. Thus, the effects of shocks on food security can be related to the food system’s structure.
Simulation of Dual Information Exposure Networks: An Agent-Based Model of Panic Buying Behavior in China
dachenga | Published Thursday, April 11, 2024The main function of this simulation model is to simulate the onset of individual panic in the context of a public health event, and in particular to simulate how an individual’s panic develops and dies out in the context of a dual information contact network of online social media information and offline in-person perception information. In this model, eight different scenarios are set up by adjusting key parameters according to the difference in the amount and nature of information circulating in the dual information network, in order to observe how the agent’s panic behavior will change under different information exposure situations.
Digital divide and opinion formation
Dongwon Lim | Published Friday, November 02, 2012 | Last modified Monday, May 20, 2013This model extends the bounded confidence model of Deffuant and Weisbuch. It introduces online contexts in which a person can deliver his or her opinion to several other persons. There are 2 additional parameters accessibility and connectivity.
MiniDemographicABM.jl: A simplified agent-based demographic model of the UK
Atiyah Elsheikh | Published Friday, July 28, 2023 | Last modified Tuesday, December 12, 2023This package implements a simplified artificial agent-based demographic model of the UK. Individuals of an initial population are subject to ageing, deaths, births, divorces and marriages. A specific case-study simulation is progressed with a user-defined simulation fixed step size on a hourly, daily, weekly, monthly basis or even an arbitrary user-defined clock rate. While the model can serve as a base model to be adjusted to realistic large-scale socio-economics, pandemics or social interactions-based studies mainly within a demographic context, the main purpose of the model is to explore and exploit capabilities of the state-of-the-art Agents.jl Julia package as well as other ecosystem of Julia packages like GlobalSensitivity.jl. Code includes examples for evaluating global sensitivity analysis using Morris and Sobol methods and local sensitivity analysis using OFAT and OAT methods. Multi-threaded parallelization is enabled for improved runtime performance.
Replication of ECEC model: Environmental Feedback and the Evolution of Cooperation
Pierre Bommel | Published Tuesday, April 05, 2011 | Last modified Saturday, April 27, 2013The model, presented here, is a re-implementation of the Pepper and Smuts’ model : - Pepper, J.W. and B.B. Smuts. 2000. “The evolution of cooperation in an ecological context: an agent-based model”. Pp. 45-76 in T.A. Kohler and G.J. Gumerman, eds. Dynamics of human and primate societies: agent-based modeling of social and spatial processes. Oxford University Press, Oxford. - Pepper, J.W. and B.B. Smuts. 2002. “Assortment through Environmental Feedback”. American Naturalist, 160: 205-213 […]
Displaying 10 of 913 results for "Gert Jan Kramer" clear search