About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 517 results for "Viet Cao" clear search
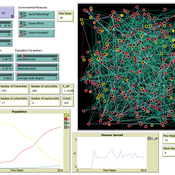
The Effect of Different Governmental Pandemic Control Measures on the Spread of a Virus Disease
Chiara Letter | Published Wednesday, January 26, 2022In this model, the spread of a virus disease in a network consisting of school pupils, employed, and umemployed people is simulated. The special feature in this model is the distinction between different types of links: family-, friends-, school-, or work-links. In this way, different governmental measures can be implemented in order to decelerate or stop the transmission.
The doctrinal paradox in deliberative process and in majority voting
Sacha Ferrari | Published Monday, January 13, 2025This model proposes a new approach analyzing to the doctrinal paradox by considering a deliberative process (which can be represented by an agent-based model) in comparison with classical (binary) majority voting and an aggregation of (continuous) degrees of belief prior to majority voting. This model is a multivariate extension of the Hegselmann–Krause opinion dynamics model.
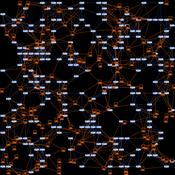
Modeling financial networks based on interpersonal trust
Michael Roos Anna Klabunde | Published Wednesday, May 29, 2013 | Last modified Thursday, November 28, 2013We build a stylized model of a network of business angel investors and start-up entrepreneurs. Decisions are based on trust as a decision making tool under true uncertainty.
Health and social public information office (SPUN) simulation
Emilio Sulis Manuela Vinai | Published Friday, November 06, 2015 | Last modified Saturday, November 07, 2015The program simulate the functioning of an italian health and social public information office (SPUN) on the basis of the real data collected in the first five years of functioning.
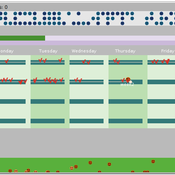
Potato late blight model
Francine Pacilly | Published Friday, April 13, 2018The purpose of the model is to simulate the spatial dynamics of potato late blight to analyse whether resistant varieties can be used effectively for sustainable disease control. The model represents an agricultural landscape with potato fields and data of a Dutch agricultural region is used as input for the model. We simulated potato production, disease spread and pathogen evolution during the growing season (April to September) for 36 years. Since late blight development and crop growth is weather dependent, measured weather data is used as model input. A susceptible and late blight resistant potato variety are distinguished. The resistant variety has a potentially lower yield but cannot get infected with the disease. However, during the growing season virulent spores can emerge as a result of mutations during spore production. This new virulent strain is able to infect the resistant fields, resulting in resistance breakdown. The model shows how disease severity, resistance durability and potato yield are affected by the fraction of fields across a landscape with a disease-resistant potato variety.
Peer reviewed FishMob: Interactions between fisher mobility and spatial resource heterogeneity
Emilie Lindkvist | Published Wednesday, October 16, 2019 | Last modified Tuesday, June 23, 2020Migration or other long-distance movement into other regions is a common strategy of fishers and fishworkers living and working on the coast to adapt to environmental change. This model attempts to understand the general dynamics of fisher mobility for over larger spatial scales. The model can be used for investigating the complex interplay that exists between mobility and fish stock heterogeneity across regions, and the associated outcomes of mobility at the system level.
The model design informed by the example of small-scale fisheries in the Gulf of California, Mexico but implements theoretical and stylized facts and can as such be used for different archetypical cases. Our methodological approach for designing the model aims to account for the complex causation, emergence and interdependencies in small-scale fisheries to explain the phenomenon of sequential overexploitation, i.e., overexploiting one resource after another. The model is intended to be used as a virtual laboratory to investigate when and how different levels of mobile fishers affect exploitation patterns of fisheries resources.
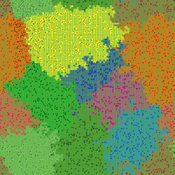
Peer reviewed Lethal Geometry
Kristin Crouse | Published Friday, February 21, 2020 | Last modified Wednesday, December 15, 2021LethalGeometry was developed to examine whether territory size influences the mortality risk for individuals within that territory. For animals who live in territoral groups and are lethally aggressive, we can expect that most aggression occurs along the periphery (or border) between two adjacent territories. For territories that are relatively large, the periphery makes up a proportionately small amount of the of the total territory size, suggesting that individuals in these territories might be less likely to die from these territorial skirmishes. LethalGeometry examines this geometric relationship between territory size and mortality risk under realistic assumptions of variable territory size and shape, variable border width, and stochastic interactions and movement.
The individuals (agents) are programmed to walk randomly about their environment, search for and eat food to obtain energy, reproduce if they can, and act aggressively toward individuals of other groups. During each simulation step, individuals analyze their environment and internal state to determine which actions to take. The actions available to individuals include moving, fighting, and giving birth.
Hybrid agent-based methodology for testing response protocols
Fernando Sancho Caparrini | Published Wednesday, February 03, 2021In recent years we have seen multiple incidents with a large number of people injured and killed by one or more armed attackers. Since this type of violence is difficult to predict, detecting threats as early as possible allows to generate early warnings and reduce response time. In this context, any tool to check and compare different action protocols can be a further step in the direction of saving lives. Our proposal combines features from continuous and discrete models to obtain the best of both worlds in order to simulate large and crowded spaces where complex behavior individuals interact. With this proposal we aim to provide a tool for testing different security protocols under several emergency scenarios, where spaces, hazards, and population can be customized. Finally, we use a proof of concept implementation of this model to test specific security protocols under emergency situations for real spaces. Specifically, we test how providing some users of a university college with an app that informs about the type and characteristics of the ongoing hazard, affects in the safety performance.
Agent-Based Model of Social Care with Kinship Networks
Umberto Gostoli Eric Silverman | Published Thursday, October 14, 2021The purpose of this model is the simulation of social care provision in the UK, in which individual agents can decide to provide informal care, or pay for private care, for their loved ones. Agents base these decisions on factors including their own health, employment status, financial resources, relationship to the individual in need and geographical location. The model simulates care provision as a negotiation process conducted between agents across their kinship networks, with agents with stronger familial relationships to the recipient being more likely to attempt to allocate time to care provision. The model also simulates demographic change, the impact of socioeconomic status, and allows agents to relocate and change jobs or reduce working hours in order to provide care.
Despite the relative lack of empirical data in this model, the model is able to reproduce plausible patterns of social care provision. The inclusion of detailed economic and behavioural mechanisms allows this model to serve as a useful policy development tool; complex behavioural interventions can be implemented in simulation and tested on a virtual population before applying them in real-world contexts.
The simulation on the study of the optimal business strategy with the interaction between technologies and consumers.
sej-yoo | Published Monday, June 27, 2022 | Last modified Monday, July 04, 2022HOW IT WORKS
This model consists of three agents, and each agent type operates per business theories as below.
a. New technologies(Tech): It evolves per sustaining or disruptive technology trajectory with the constraint of project management triangle (Scope, Time, Quality, and Cost).
b. Entrepreneurs(Entre): It builds up the solution by combining Tech components per its own strategy (Exploration, Exploitation, or Ambidex).
c. Consumer(Consumer): It selects the solution per its own preference due to Diffusion of innovation theory (Innovators, Early Adopters, Early Majority, Late Majority, Laggards)
…
Displaying 10 of 517 results for "Viet Cao" clear search