About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 494 results for "Jingjing Cai" clear search
The Hawk-Dove Game
Kristin Crouse | Published Tuesday, November 05, 2019This model simulates the Hawk-Dove game as first described by John Maynard Smith, and further elaborated by Richard Dawkins in “The Selfish Gene”. In the game, two strategies, Hawks and Doves, compete against each other, and themselves, for reproductive benefits. A third strategy can be introduced, Retaliators, which act like either Hawks or Doves, depending on the context.
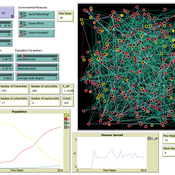
COVID-19 ABM
Gudrun Wallentin | Published Tuesday, April 21, 2020 | Last modified Tuesday, April 21, 2020Model of the Corona pandemic outbreak
The COVID-19 ABM aims to predict the qualitative behaviour of the CoViD-19 epidemic dynamics for the greater region of Salzburg City. Specifically, by means of scenario testing, it aims to help assessing how containment interventions can allow a stepwise relaxation of the lockdown without risking a new outbreak.
Virus Spread on Broad-degree-distribution Network.
Gianluca Manzo | Published Friday, July 24, 2020The model simulates the spread of a virus through a synthetic network with a degree distribution calibrated on close-range contact data. The model is used to study the macroscopic consequences of cross-individual variability in close-range contact frequencies and to assess whether this variability can be exploited for effective intervention targeting high-contact nodes.
The Agent-Based Wildfire Simulation Environment (ABWiSE) translates the concept of a moving fire front as a set of mobile fire agents that respond to, and interact with, vegetation, wind, and terrain. Presently, the purpose of ABWiSE is to explore how ABM, using simple interactions between agents and a simple atmospheric feedback model, can simulate emergent fire spread patterns.
The Effect of Different Governmental Pandemic Control Measures on the Spread of a Virus Disease
Chiara Letter | Published Wednesday, January 26, 2022In this model, the spread of a virus disease in a network consisting of school pupils, employed, and umemployed people is simulated. The special feature in this model is the distinction between different types of links: family-, friends-, school-, or work-links. In this way, different governmental measures can be implemented in order to decelerate or stop the transmission.
The doctrinal paradox in deliberative process and in majority voting
Sacha Ferrari | Published Monday, January 13, 2025This model proposes a new approach analyzing to the doctrinal paradox by considering a deliberative process (which can be represented by an agent-based model) in comparison with classical (binary) majority voting and an aggregation of (continuous) degrees of belief prior to majority voting. This model is a multivariate extension of the Hegselmann–Krause opinion dynamics model.
Modeling financial networks based on interpersonal trust
Michael Roos Anna Klabunde | Published Wednesday, May 29, 2013 | Last modified Thursday, November 28, 2013We build a stylized model of a network of business angel investors and start-up entrepreneurs. Decisions are based on trust as a decision making tool under true uncertainty.
Health and social public information office (SPUN) simulation
Emilio Sulis Manuela Vinai | Published Friday, November 06, 2015 | Last modified Saturday, November 07, 2015The program simulate the functioning of an italian health and social public information office (SPUN) on the basis of the real data collected in the first five years of functioning.
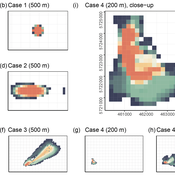
Potato late blight model
Francine Pacilly | Published Friday, April 13, 2018The purpose of the model is to simulate the spatial dynamics of potato late blight to analyse whether resistant varieties can be used effectively for sustainable disease control. The model represents an agricultural landscape with potato fields and data of a Dutch agricultural region is used as input for the model. We simulated potato production, disease spread and pathogen evolution during the growing season (April to September) for 36 years. Since late blight development and crop growth is weather dependent, measured weather data is used as model input. A susceptible and late blight resistant potato variety are distinguished. The resistant variety has a potentially lower yield but cannot get infected with the disease. However, during the growing season virulent spores can emerge as a result of mutations during spore production. This new virulent strain is able to infect the resistant fields, resulting in resistance breakdown. The model shows how disease severity, resistance durability and potato yield are affected by the fraction of fields across a landscape with a disease-resistant potato variety.
Peer reviewed FishMob: Interactions between fisher mobility and spatial resource heterogeneity
Emilie Lindkvist | Published Wednesday, October 16, 2019 | Last modified Tuesday, June 23, 2020Migration or other long-distance movement into other regions is a common strategy of fishers and fishworkers living and working on the coast to adapt to environmental change. This model attempts to understand the general dynamics of fisher mobility for over larger spatial scales. The model can be used for investigating the complex interplay that exists between mobility and fish stock heterogeneity across regions, and the associated outcomes of mobility at the system level.
The model design informed by the example of small-scale fisheries in the Gulf of California, Mexico but implements theoretical and stylized facts and can as such be used for different archetypical cases. Our methodological approach for designing the model aims to account for the complex causation, emergence and interdependencies in small-scale fisheries to explain the phenomenon of sequential overexploitation, i.e., overexploiting one resource after another. The model is intended to be used as a virtual laboratory to investigate when and how different levels of mobile fishers affect exploitation patterns of fisheries resources.
Displaying 10 of 494 results for "Jingjing Cai" clear search