About the CoMSES Model Library more info
Our mission is to help computational modelers at all levels engage in the establishment and adoption of community standards and good practices for developing and sharing computational models. Model authors can freely publish their model source code in the Computational Model Library alongside narrative documentation, open science metadata, and other emerging open science norms that facilitate software citation, reproducibility, interoperability, and reuse. Model authors can also request peer review of their computational models to receive a DOI.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with additional detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 103 results for "Steven Dalderop" clear search
Peer reviewed Are Countertrade credits as flexible and efficient as cash? A novel approach to reducing income inequality using countertrade methodology.
Peter Malliaros | Published Monday, May 03, 2021 | Last modified Tuesday, May 11, 2021The impacts of income inequality can be seen everywhere, regardless of the country or the level of economic development. According to the literature review, income inequality has negative impacts in economic, social, and political variables. Notwithstanding of how well or not countries have done in reducing income inequality, none have been able to reduce it to a Gini Coefficient level of 0.2 or less.
This is the promise that a novel approach called Counterbalance Economics (CBE) provides without the need of increased taxes.
Based on the simulation, introducing the CBE into the Australian, UK, US, Swiss or German economies would result in an overall GDP increase of under 1% however, the level of inequality would be reduced from an average of 0.33 down to an average of 0.08. A detailed explanation of how to use the model, software, and data dependencies along with all other requirements have been included as part of the info tab in the model.
Agent-based model of team decision-making in hidden profile situations
Jonas Stein Andreas Flache Vincenz Frey | Published Thursday, April 20, 2023 | Last modified Friday, November 17, 2023The model presented here is extensively described in the paper ‘Talk less to strangers: How homophily can improve collective decision-making in diverse teams’ (forthcoming at JASSS). A full replication package reproducing all results presented in the paper is accessible at https://osf.io/76hfm/.
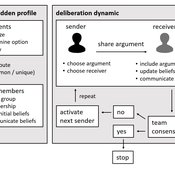
Narrative documentation includes a detailed description of the model, including a schematic figure and an extensive representation of the model in pseudocode.
The model develops a formal representation of a diverse work team facing a decision problem as implemented in the experimental setup of the hidden-profile paradigm. We implement a setup where a group seeks to identify the best out of a set of possible decision options. Individuals are equipped with different pieces of information that need to be combined to identify the best option. To this end, we assume a team of N agents. Each agent belongs to one of M groups where each group consists of agents who share a common identity.
The virtual teams in our model face a decision problem, in that the best option out of a set of J discrete options needs to be identified. Every team member forms her own belief about which decision option is best but is open to influence by other team members. Influence is implemented as a sequence of communication events. Agents choose an interaction partner according to homophily h and take turns in sharing an argument with an interaction partner. Every time an argument is emitted, the recipient updates her beliefs and tells her team what option she currently believes to be best. This influence process continues until all agents prefer the same option. This option is the team’s decision.
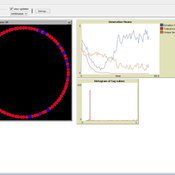
Models associated with paper entitled "Polarization in Social Media: A Virtual Worlds-Based Approach"
Dennis Jacob Sven Banisch | Published Thursday, June 22, 2023This model contains MATLAB code describing the virtual worlds framework used in the paper entitled “Polarization in Social Media: A Virtual Worlds-Based Approach.” The parent directory contains driver code for replicating results from the paper. Additionally, the source code is structured by three directories:
- Data Structures: Contains classes and objects used in the code, such as the virtualWorlds.m
- Metrics: Contains code which computes metrics, such as congruentLinks.m
- Visualization: Contains code for generating pictures and plots, such as drawSystemState.m
…
Last Mile Commuter Behavior Model
Moira Zellner Dean Massey Yoram Shiftan Jonathan Levine Maria Arquero | Published Friday, November 07, 2014 | Last modified Friday, November 07, 2014We represent commuters and their preferences for transportation cost, time and safety. Agents assess their options via their preferences, their environment, and the modes available. The model has policy levers to test impact on last-mile problem.
Spatial model of the noisy Prisoner's Dilemma with reward shift
Matus Halas | Published Thursday, March 05, 2015 | Last modified Tuesday, May 29, 2018Interactions of players embedded in a closed square lattice are determined by distance and overall gains and they lead to shifts of reward payoff between temptation and punishment. A new winner balancing against threats is ultimately discovered.
Hybrid agent-based methodology for testing response protocols
Fernando Sancho Caparrini | Published Wednesday, February 03, 2021In recent years we have seen multiple incidents with a large number of people injured and killed by one or more armed attackers. Since this type of violence is difficult to predict, detecting threats as early as possible allows to generate early warnings and reduce response time. In this context, any tool to check and compare different action protocols can be a further step in the direction of saving lives. Our proposal combines features from continuous and discrete models to obtain the best of both worlds in order to simulate large and crowded spaces where complex behavior individuals interact. With this proposal we aim to provide a tool for testing different security protocols under several emergency scenarios, where spaces, hazards, and population can be customized. Finally, we use a proof of concept implementation of this model to test specific security protocols under emergency situations for real spaces. Specifically, we test how providing some users of a university college with an app that informs about the type and characteristics of the ongoing hazard, affects in the safety performance.
Using Agent-Based Modelling and Reinforcement Learning to Study Hybrid Threats
kpadur | Published Friday, September 20, 2024Hybrid attacks coordinate the exploitation of vulnerabilities across domains to undermine trust in authorities and cause social unrest. Whilst such attacks have primarily been seen in active conflict zones, there is growing concern about the potential harm that can be caused by hybrid attacks more generally and a desire to discover how better to identify and react to them. In addressing such threats, it is important to be able to identify and understand an adversary’s behaviour. Game theory is the approach predominantly used in security and defence literature for this purpose. However, the underlying rationality assumption, the equilibrium concept of game theory, as well as the need to make simplifying assumptions can limit its use in the study of emerging threats. To study hybrid threats, we present a novel agent-based model in which, for the first time, agents use reinforcement learning to inform their decisions. This model allows us to investigate the behavioural strategies of threat agents with hybrid attack capabilities as well as their broader impact on the behaviours and opinions of other agents.
Foundress dilemma model
Zachary Joseph Shaffer Takao Sasaki Brian Haney Marco Janssen Stephen Pratt Jennifer Fewell | Published Thursday, July 28, 2016A haystack-style model of group selection to capture the essential features of colony foundation for queens of the ant based on observation of the ant Pogonomyrmex californicus.
Concession Forestry Modeling
Andrew Bell Rick L Riolo Jacqueline M Doremus Daniel G Brown Thomas P Lyon John Vandermeer Arun Agrawal | Published Thursday, January 23, 2014A logging agent builds roads based on the location of high-value hotspots, and cuts trees based on road access. A forest monitor sanctions the logger on observed infractions, reshaping the pattern of road development.
The emergence of tag-mediated altruism in structured societies
Shade Shutters David Hales | Published Tuesday, January 20, 2015 | Last modified Thursday, March 02, 2023This abstract model explores the emergence of altruistic behavior in networked societies. The model allows users to experiment with a number of population-level parameters to better understand what conditions contribute to the emergence of altruism.
Displaying 10 of 103 results for "Steven Dalderop" clear search